I use linux. I prefer it over Windows for many reasons. It’s more resistant to viruses, less of a target, but that doesn’t mean that malware or other viruses are impossible. If someone were to trick me into running something and even worse, trick me into using my administrator password to install something system wide, it could be the same end result as a windows malware infection. To be fair Microsoft has improved their security over the years. They are still the most likely platform though to get a drive by virus just by visiting a site (with no user interaction.) That much said, Mac users and Linux users should avoid being smug. Why? They aren’t completely safe. No one is. Social engineering is the most common (and most effective) path to getting malware on a computer.
[ad#adsensesquare]
I’ve done computer service for a number of years. Mostly small groups, home users, small businesses. But sometimes at larger organizations. It has many times amazed me that people let me at their computer by explaining that I’m there to look at the computers and _________ sent me back. I many times remember Face from the A-team…. “Hi I’m billy bob and this is my assistant sparky – we had a trouble ticket filed about the _______ and need to check out your workstation.” I can’t think of any time that I ran into someone new that wanted to call and check with someone else. Not once in ~15 years.
Recently there’s news of Mac Shield a malware for the mac that resembles rogue antivirus software on windows. Apparently a popup appears claiming that your mac has an infection and your administrator password is needed to remove it. Once it receives the administrator password…. game over you NOW have malware and it’s going to serve up illicit content over a public webserver, it’s going to collect passwords, bank account logins, credit card numbers and who knows what else on your nice secure smug mac.
The key learning moment here should be that it’s the user that was vulnerable – not the system!
Smugness should step aside.
Now, if you’re a mid size company that hires outside computer help – do you have a procedure for making sure that the person showing up is who they say they are? if you are large enough for an in house it department – are there name tags and ways to know that this guy that says he’s “the new guy” in IT really IS with your company?
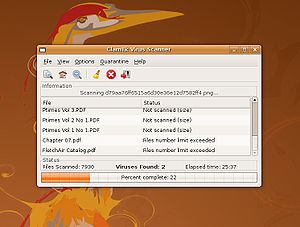
Unfortunately in most organizations you can’t have a quick look from an IT person everytime you have a popup claiming that you have a virus. So, it’s important to become familiar with the legitimate popups of your antivirus software so you can discern better what is authentic and what isn’t. Sorry, but even that is no silver bullet. The malware writers are clever and who knows they may find a way to mimic whatever is preinstalled on the system for antivirus.
